What’s new in OpenWrt 22.03?
OpenWrt 22.03 will be out soon - whats new? nftables will replace iptables - what are the impacts? How about upgrading OpenWrt? Added Wifi-6 support? We’ll look at the OpenWrt user interface (LuCI) for apparent changes, go through the OpenWrt change log and have a look at upgrading OpenWrt. The OpenWrt firewall change is the top change in this version.
 Watch the video on YouTube
Watch the video on YouTube
Click to view the entire transcript
Recently most comments on my OpenWrt videos are saying something like “Marc, can you make an update video? OpenWrt Version 22 is on the horizon. So – here it comes. OpenWrt Version 22. I first want to have a look at a fresh clean install and check if there are any major differences or new things. We will then check the change logs of the project in order to see what’s new and last but not least we’ll have a quick look at the upgrade process.
(optional)
At the time of making this video, in July 2022, there was no final release yet. Release Candidate 5 was out and Release Candidate 6 was just in the build process on August 1st. Therefore, all screen cams are made with the Release candidate 22.03 rc5. That was released on July 8th. So it’s still a moving target after all.
(clean new install, changes)
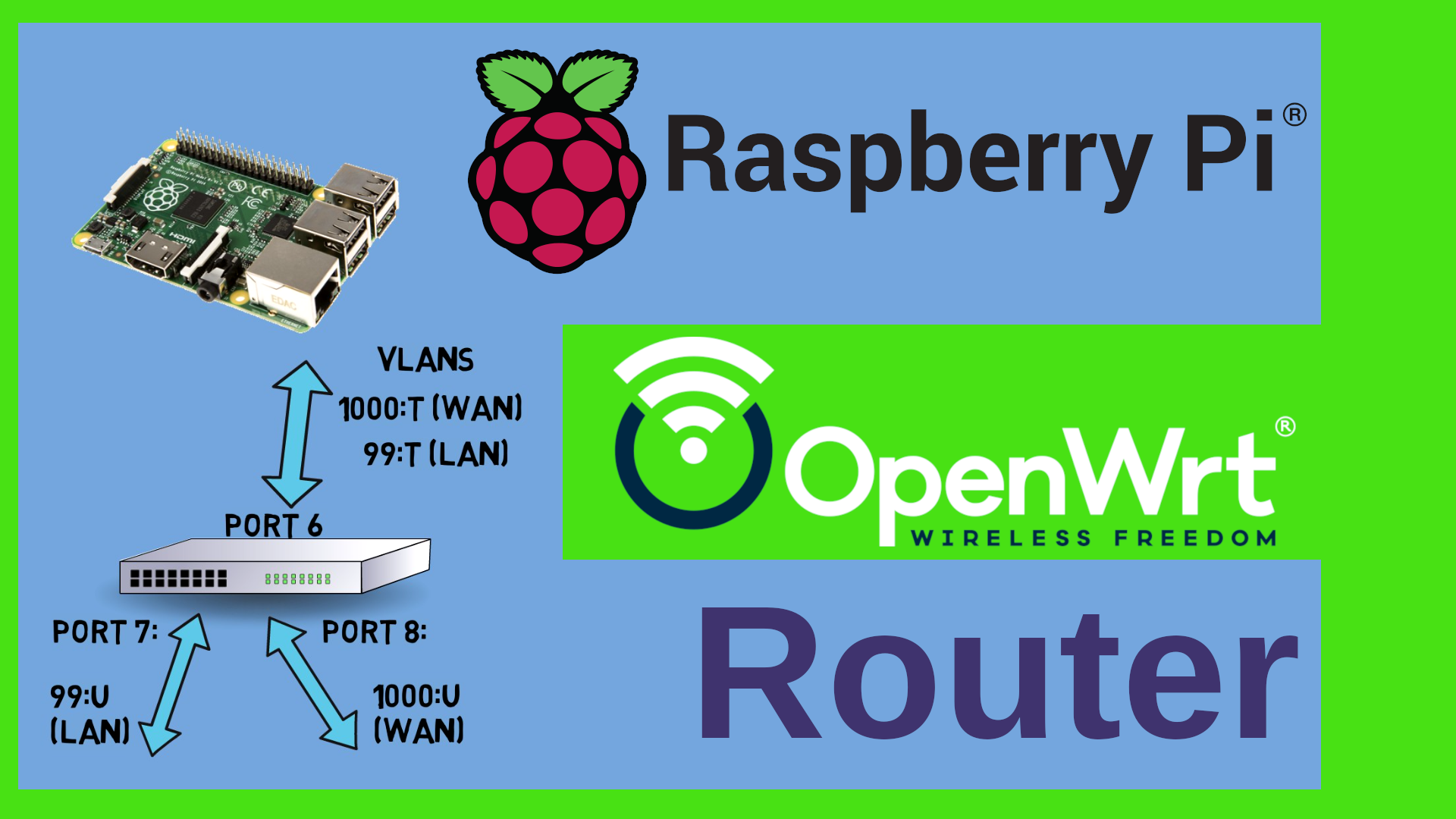
I have downloaded and installed the 64bit x86 version into my Proxmox Sandbox. This is a clean new install, so there were no hick ups with regards to the installation really. Let’s have a look at the OpenWrt user interface which is called LuCi and see if we can spot any changes. Guys, just a reminder – the OpenWrt software on one side and the Web interface on the other side are two distinct projects, right? You can find both on the OpenWrt github, one in the openwrt repo and the other in the luci repo. Very often people who don’t like OpenWrt mostly refer to its user interface – LuCi rather than to OpenWrt itself. On the other side, Devices that are sold under a certain brand like – I don’t know – Linksys, Netgear, Asus – you name any vendor – sometimes come in different revisions of the same product name. And it may be that revision 1 and 2 are using a certain hardware and revisions 3 and 4 are totally different devices, but they have the same case and the same user interface. In LuCi, the web interface can change depending on the number of software modules that you have installed. I guess the point that I want to make is “don’t judge a book by its cover”. Anyway, let’s move on.
Looking at a vanilla installation of OpenWrt and LuCi, at a first glance there aren’t really any big apparent changes. I could only find three or four. And those are mainly related to one of the rather bigger changes in this version. But let’s first have a look at them. If you click on Status and then Firewall, you can see that the overview page here has changed. In previous versions you could see a lot of entries under each table here. Now we have a different view that shows basically two columns – and those are titled “Rule matches” and “Rule actions”. I’ll explain everything. Let’s keep looking for the moment. The next apparent change in OpenWrt 22 is if we go to Network – then DHCP and DNS. There are two new tabs here called “IP Sets” where apparently we can define a number of IP addresses and group them together in a domain. Then there is this tab called Hostnames. And I’ve been waiting for this one really. Because dnsmasq is at the same time a dhcp and dns server. And if you have static dhcp leases then they are also reflected in dns. But sometimes you just want to make a dns entry without dhcp. You can do that now here. There is another change here. The TFTP tab has been renamed to PXE/TFTP. And if you enable it then you have additional options for PXE booting. Guys, let me know in the comments if you want a video on network boot. Interesting feature. Last but not least, there is a tiny difference in the firewall menu under Network- Firewall. The tab for custom rules seems to have vanished.
So – what do these changes reflect – or what are they good for? Let’s have a look at the Change logs on the OpenWrt project page and things will become clear.
But wait – we’ll do that right after this call to action! I really need you to get involved please! First off – if you like the video so far and if you like my OpenWrt videos, then a like on YouTube is really appreciated! A comment on YouTube would be top of the pop! I really try to answer everyone! Also – I very often get questions like “Marc, can we support you?” Yes, you actually can, in multiple ways. You know that I am on Patreon, so if you want to become a Patron – feel free to support the channel there. You’ll hold a very special place in my heart if you do. But there’s also many other ways to support the channel and keep it independent of sponsors. If you like a video, then please copy the link of the video and post about it in forums. I can’t do that. It’s considered to be self promotion on many platforms such as Reddit or Facebook if I do. But you can. Please do talk about my videos and about my channel to others. Feel free to link to my videos from your blogs. That would be really amazing – last but not least – I run a discord server – the invitation link is in the description – if you join the server then you can talk to me and the folks there every Sunday 9 AM and 6 PM Berlin / Paris time. Live. Thanks so much guys! Back to OpenWrt.
Most of the changes that you see here should not really affect you if you are not running any very specific software module on your router. There’s loads of changes that are linux specific such as the versions of the toolchains used and so on. However, these changes are important and they confirm my decision to move to OpenWrt. It is utterly important that linux components are updated regularly because of security vulnerabilities. Cheap consumer routers typically don’t get any updates from the vendor any more after a certain time. Also I am glad that the year 2038 problem has been solved and that we now have another 292 billion years before the next YsomethingK bug shows up. Pun intended. More good news slightly above – More targets now support Distributed switch architecture – DSA and over 160 devices have been added since version 21 so that the total number of OpenWrt supported devices now exceeds 1550. I let that sink for a second. The top change here however is the one that is related to what we saw in the LuCi interface. The OpenWrt firewall has changed from fw3 with iptables to fw4 with nftables. What’s the impact of this?
The good news is – the average user should not be impacted at all. There are various layers that assure compatibility with the previous fw3 firewall. Let’s go through them quickly. First – the user interface. Nothing has changed here. You define the rules just like you did before. That’s a good thing. Next let’s look at the config files. Let’s have a look at a /etc/config/firewall file. Nothing has changed here neither. So if you have scripts running that relate on uci as an interface then you should be good to migrate without changes. Now let’s look at the fw3 and fw4 binaries. As you can see here, the fw3 binary has just been replaced by a symlink to the fw4 binary. That’s also a good thing. If you have scripts running fw3 then presumably you don’t even have to change them. Now for the iptables binary. What if you run scripts that use the iptables command? Well, in a vanilla installation that binary does not exist any more. But fear not. You can actually install the software package iptables-nft and look what that does: it actually created a symlink again from /usr/sbin/iptables to the binary xtables-nft-multi. Now – as the chains and tables do not necessarily have to have the same names here, I understand that the iptables –list or –list-rules does not show anything. What if we create a simple iptables entry? Will it be added to the nftables rulesets ? In fact, if it is a simple rule like I did here – reject a certain source IP – then yes, it will be added to nft. If however you use a more complex rule that can not be easily translated, then this rule will end up in legacy iptables. So that’s definitely something to keep in mind. If you are adding iptables rules by hand, those will presumably interfere with nftables. That may change, but I would really suggest you migrate them to nftables. Mixing both does really NOT look like a good idea to me. Unless you really really know what you are doing.
On that note – nftables. Initially I had planned to give you guys more insight into nftables and maybe how to use the nft command. But a part of the work that I do before I publish a video is research. I want to make sure that what I tell you in the video is correct and also I want to see if anyone else has already made a video on the subject. If I find videos and I think that I can make them better, then I go for it. On the other hand, if another creator has put work and thought into a video and I like it, then there is absolutely no point in me making another video about the same matter, right? And this is the case for nftables. A fellow YouTuber named Vineet has made two videos about nftables which I really like on his channel XPSTECH. I put the link up here and in the description. Surprisingly, these videos don’t have that many views and also very few comments. Totally underrated. If you want to know more about nftables, then please check out Vineet’s videos. Show him some love and give his videos a like and also – please DO leave him a comment. Those videos only have 10 comments or so. Many thanks for that! But DO come back here after that right?
However, there is one point or maybe actually two or three about nftables that I want to quickly emphasize on. The first one is that nftables does not have a rigid predefined table and chain structure like iptables. You could essentially create tables and chains and name them as you want. You can also define rules and jump from one rule to another. But to me the biggest advantage is that nftables by design knows ipv4, ipv6 or both combined as a protocol. If I wanted to define a rule in iptables, then I would have to create two rules. One with iptables and one with ip6tables. With nftables it’s only one rule that I have to create. Guys, if you still want me to make some update video on nftables and firewall with OpenWrt then please let me know in the comments!
Awesome – now let’s have a look at upgrading. You can’t upgrade directly from version 19 to 22. I mean, you can but you will lose some configuration of your router. If you upgrade on a target that had the old swconfig switch configuration and now supports DSA, then this part of the config might be lost. You will have to reapply it. Let me upgrade my Belkin RT3200 Wi-fi 6 router from an OpenWrt 21 snapshot to OpenWrt 22 release candidate. First I pick the image file from the OpenWrt Firmware selector. Then all I have to do really is go to system-backup/flash firmware, scroll down to Flash Image, select the file that I downloaded from OpenWrt.org and klick on upload. If that procedure fails (which may sometimes happen on the snapshot versions of OpenWrt), then alternatively I can ssh into the router, cd into the /tmp directory, then download the image from OpenWrt to the /tmp directory and launch sysupgrade from there. As this device is acting as access point only, there is no impact with regards to firewall. The firewall is switched off here. However, this router is a Wifi 6 router with Mediatek hardware. And that means that I do get all the updates from the Wifi repos such as – in my case – the mt76 repo – look at the changes in the change log here. That’s another thing to note really – even if you don’t notice any changes in the user interface, there will always be loads of fixes, patches and upgrades under the hood. For me and my Belkin there are three relevant sections here – the Target /media, the Wireless/common, the mt76 driver section and – of course – the addressed bugs and security fixes.
Guys, there will be a separate video on upgrading OpenWrt. Doing an upgrade on a single wired Access point is simple, but there are other use cases such as x86 or Mesh points that need a bit more preparation and Thinking. Watch out for that.
Awesome – that’s it for today. Thank you so much for watching. And – as always – stay safe, stay healthy, bye for now!

 Watch the video on YouTube
Watch the video on YouTube